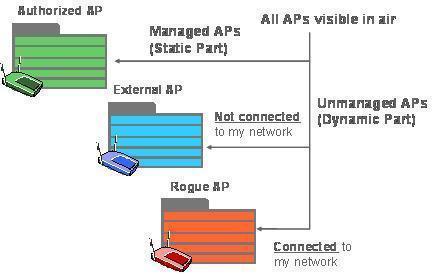
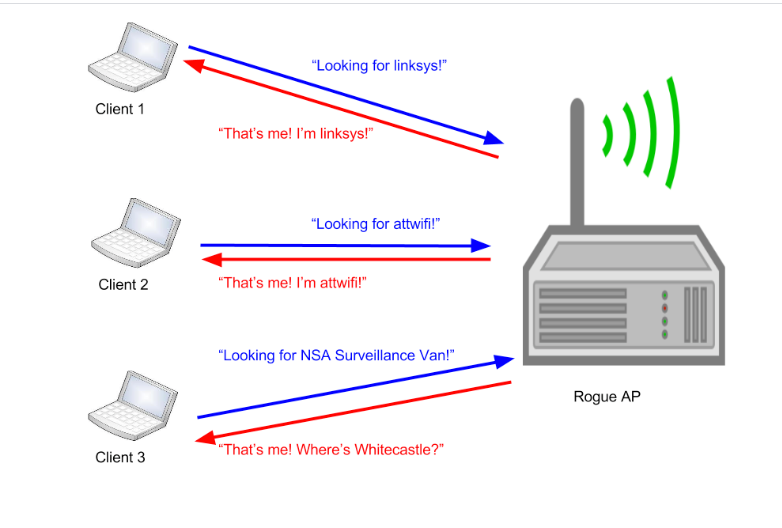
![Unsecured Rogue Access Point Allows Anyone to Connect to the Network [17] | Download Scientific Diagram Unsecured Rogue Access Point Allows Anyone to Connect to the Network [17] | Download Scientific Diagram](https://www.researchgate.net/publication/276230435/figure/fig3/AS:668979894951955@1536508644638/Unsecured-Rogue-Access-Point-Allows-Anyone-to-Connect-to-the-Network-17.jpg)
Unsecured Rogue Access Point Allows Anyone to Connect to the Network [17] | Download Scientific Diagram
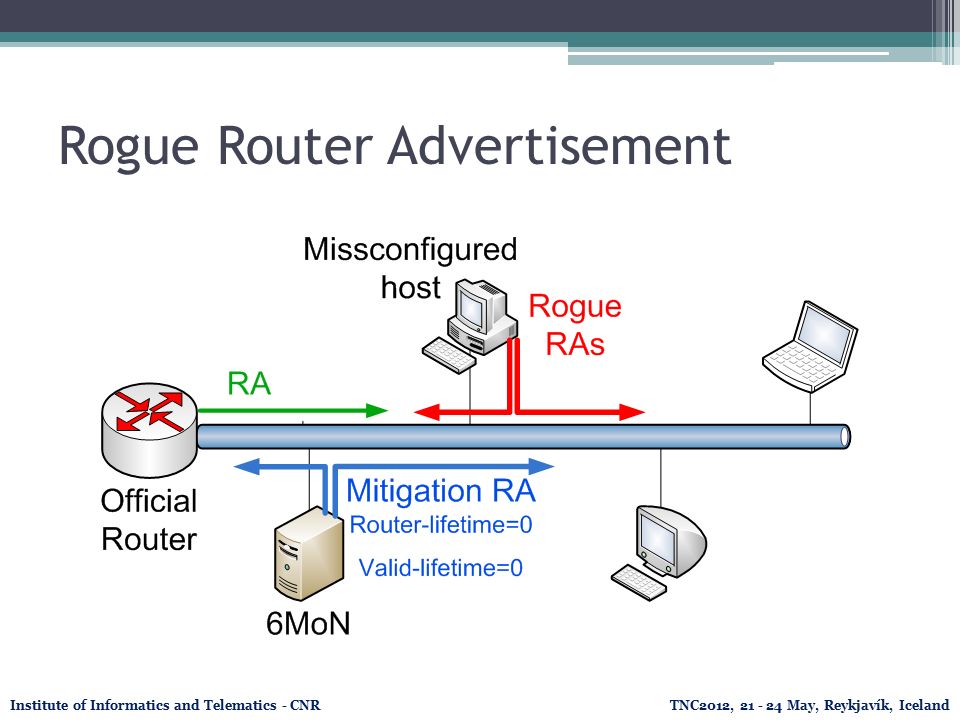
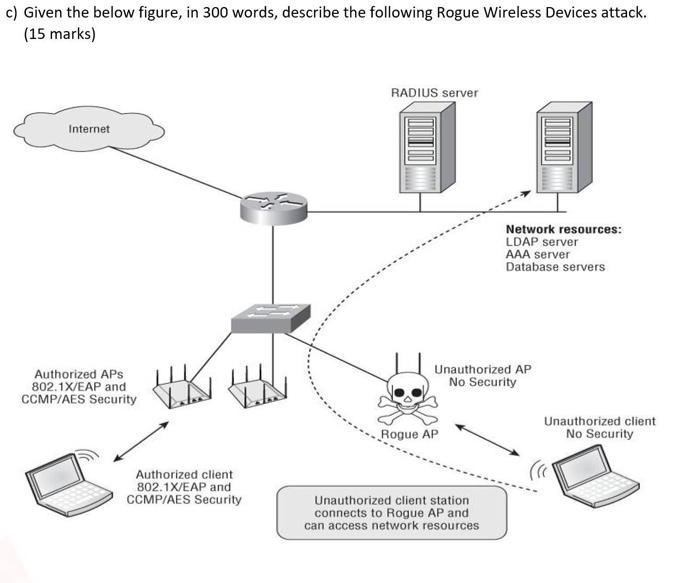
6Mon: Rogue IPv6 Router Advertisement detection and mitigation and IPv6 address utilization network monitoring tool Institute of Informatics and Telematics. - ppt download




![PDF] A Review of Online Rogue Access Point Detection | Semantic Scholar PDF] A Review of Online Rogue Access Point Detection | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/d0ed1b76a7acad87e8bb816c84444e4cf6a64b7c/2-Figure1-1.png)